Portfolio: LEAP™ 5 Content Management System
LEAP™ 5 - a ground up reimagining of Content Management, meant as a secure, flexible and extensible platform alternative to WordPress, Drupal and Plone, aimed at the SME sector.
This project was begun in August of 2009, and leveraged the then-beta Lasso 9.0. While the core development of LEAP™ 5 was complete November of 2010, the system has undergone significant upgrades since and is on it's third major revision (5.2) and was publicly released alongside Lasso 9.3 in January 2015.
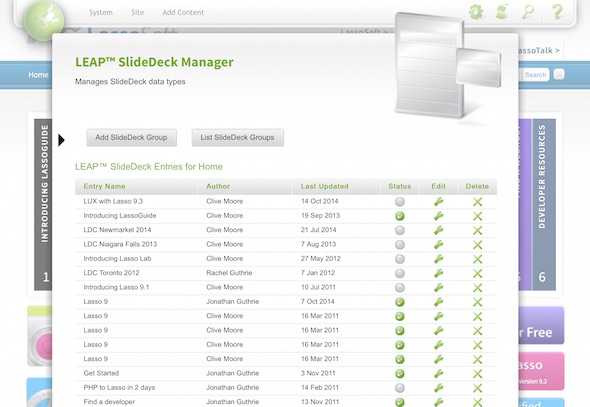
The system is designed as a modular series of compiled "LassoApps" which drop into a Lasso 9 instance (a run-time container), which instantly transform the system into a CMS through a Web-UI installer.
LEAP™ 5.2 has been included as a 1-click install in the Lasso Server 9.3 release.
Role: Project Architect & Lead Developer
Responsible as Project Architect for the imagining of the technical design, pushing the boundaries of the Lasso 9 language which was in beta when the project was initiated.
Ongoing involvement as Lead Developer during the maintenance and evolution phase of the system since initial launch, and doing this alongside working on the Lasso language led to being able to leverage the foundations of the language to achieve stellar stability and performance.
Scope
The initial specification included a level of compatibility with the previous version of the system, which meant the database schema needed as much commonality as possible, with clear upgrade processes to the new schema.
The system was also designed to include:
- easy configuration and management by non-technical staff
- multiple levels of administration access
- security "zones" for both administration and authenticated public users
- built in form management
- multiple site management
- mulilingual capacity
- modular content and adminisration plugins
- ability to run compiled be default, but also as "open" uncompiled code for developement and site-specific plugins
- high availability compatibility
- secure administration is via authenticated overlay, not URL-based to decrease the attack surface of the system